Secure your cloud journey at every phase.
Cloud Vulnerabilities: Challenges With Securing Your Data
The complexity involved in managing disparate solutions securely on the cloud heightens the risk of various security breaches, such as automated hacking. This is made even easier because of the use of default credentials, and easy-to-connect remote access to the cloud.
Protecting your enterprise’s cloud data from threats and vulnerabilities is a complex venture that requires the right partner to effectively orchestrate and execute. As a digital consulting services firm, Trianz is well-versed in cloud solutions and has conducted numerous successful cloud security engagements.
Our cloud security strategy will ensure:
- Data privacy and encryption in the cloud
- In-depth defense with DLP, PAM, anti-malware and ransomware protection tools
- Self-determined threat reaction and response
- Security analytics
- Self-defending, AI-enabled security systems
Olympic has built one of the world’s largest databases on cloud and digital research, with data from more than 5,000 companies spanning 20 industries.
We understand the state of cloud security, investment priorities, the latest technologies and the best practices followed by the most successful companies in the world.
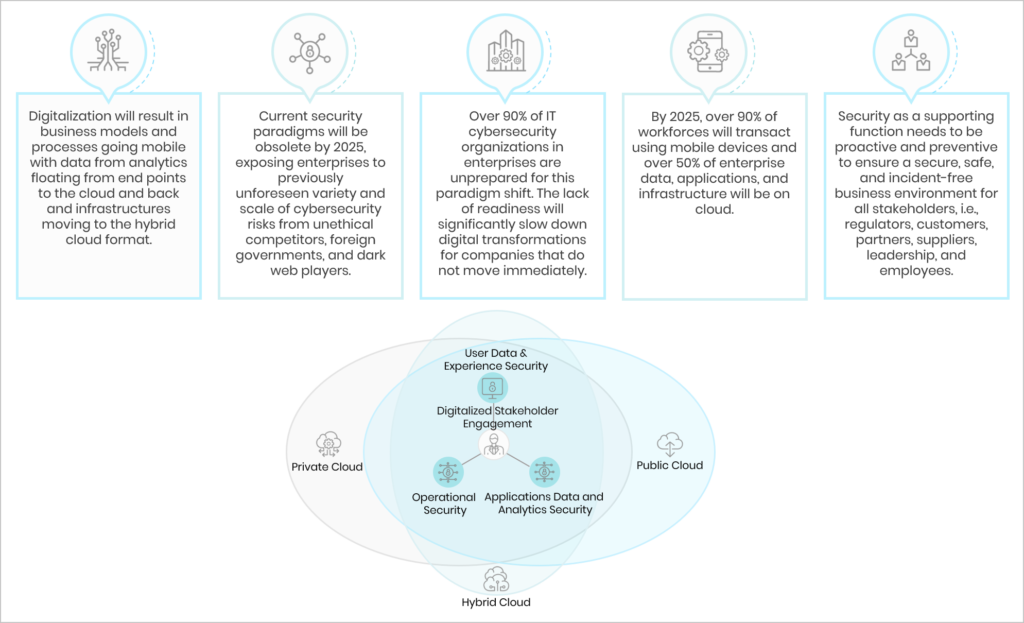
The Role of Cybersecurity
Our Cloud Security Services
As your partner, Olympic will work closely with you so we can create a solution that is tailored to your organization’s and stakeholders’ requirements while also being well-thought-out and regulation-compliant. Our services entail:
Security Assessment and Recommendation
- Assessment and recommendations based on existing security posture
- Current-state scorecard and gap analysis
- Evaluation and recommendation of best solutions to eliminate cyber security risks
- Establishment of an overarching security engineering and operations strategy
Security-integrated Product Engineering
- Built in collaboration with your engineering team, resulting in a reduction of security flaws and vulnerabilities
- Implementation of defensive and preventive mechanisms to protect digital footprint, including data networks, applications, and intellectual property
Data Encryption and Protection
- Storage protection
- Encryption in-use, rest and at-transit
- Key management service and cloud-based hardware security module (HSM)
Our Approach to Cloud Security
We begin by building a cloud security roadmap to guide the deployment, making sure to align it with end-to-end business and technology requirements. Our cloud security strategy is therefore designed to ensure that both IT and business are on the same page throughout.
The team will then develop a plan to ensure that the security policies are smoothly implemented, increasing extant security measures, your security posture and regulatory compliance, while also reducing infrastructure spend.